This is follow up on prior comment/post
https://forums.hardwarezone.com.sg/threads/ipv6-discussions.6976522/post-157322145
and on Singtel fibre broadband home:
the old setup of using 6RD Border Relay: 6rd.singnet.com.sg (202.166.127.6)
https://forums.hardwarezone.com.sg/threads/ipv6-discussions.6976522/#post-150382982
it seemed no longer works
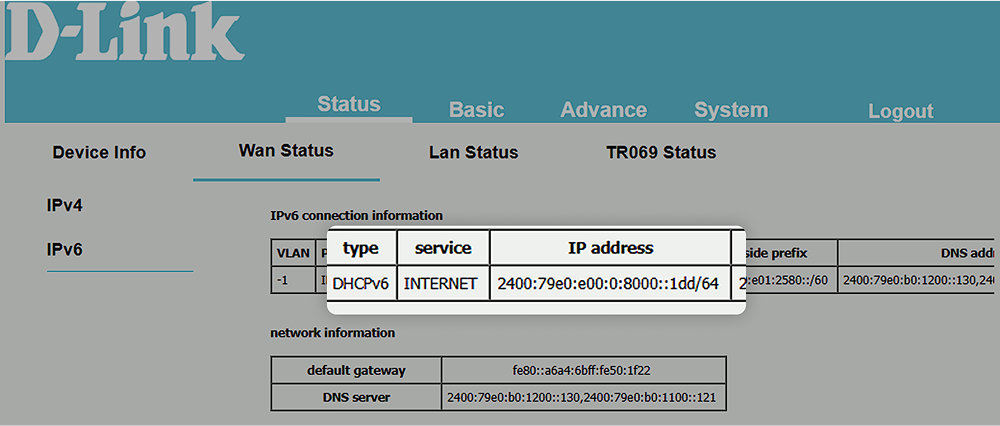
I tried setting up my router (actually a pc runninig linux) , apparently Singtel now uses "dual stack"
quite similar to 'other' ISPs I suppose. i.e. DHCPv6
> dhclient -6 -v eno1.10
Internet Systems Consortium DHCP Client 4.4.1
Copyright 2004-2018 Internet Systems Consortium.
All rights reserved.
For info, please visit https://www.isc.org/software/dhcp/
Listening on Socket/eno1.10
Sending on Socket/eno1.10
PRC: Confirming active lease (INIT-REBOOT).
XMT: Forming Confirm, 0 ms elapsed.
XMT: X-- IA_NA xx:yy
XMT: | X-- Confirm Address 2400:d802:xxxx:yyyy::zz
XMT: V IA_NA appended.
XMT: Confirm on eno1.10, interval 1030ms.
RCV: Reply message on eno1.10 from fe80::xxxx:yyyy.
RCV: X-- Server ID: 00:01:xxxx
message status code Success: "All addresses are on-link"
PRC: Bound to lease 00:01:xxxx.
^ it is quite strange the reply from came an fe80 address of the dhcp server.
something more about that fe80:: address
https://en.wikipedia.org/wiki/Link-local_address#IPv6
fe80:: addresses are "link local" addresses, supposedly don't pass across routers.
if say ISP (e.g. Singtel) 'cut off' *firewall* rest of internet from sending from arbitrary fe80:: address,
then it is safe for you to say only if my router see DHCP address from fe80:: xxxx I trust, i.e. they cannot spoof (pretend to be) that fe80:: (DHCP server) if ISP drop them. then your firewall rule should only accept *IPV6* DHCPv6 (port 546) from dhcp servers starting wiith address fe80:: .
These days one needs to be paranoid about security, anything that you don't firewall enough is open buffet for hackers, crackers, viruses, ransomware, state sponsored attackers.
15: eno1.10@eno1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 state UP qlen 1000
inet6 2400:d802:xxxx:yyyy::zz/128 scope global
there is catch, initially it didn't work
you need to open ipv6 port 546 (only ipv6 !) and better restrict (firewall to trusted one) the IP address of the DHCPv6 server or in theory anyone can give you an ipv6 address, and maybe hack your host into the dark side internet.
so that is /128
1 out of 340,282,366,920,938,463,463,374,607,431,768,211,456, addresses, a bit of a miser?
https://en.wikipedia.org/wiki/IPv6
still very early in my experiments, many 'problems' to solve
need to figure out how do to 'delegation' can take /64 or better /56 ?
btw for those who did not figure this out if you get /64 (lower 64 bits) or /56 (lower 72 bits) that is more than 4 billion times the whole IPv4 internet, not 16 billion, instead that number at 64 bits is 18,446,744,073,709,551,616, even lottery cannot fight this.
but the urban legend in the ipv6 age SLAAC
https://www.networkacademy.io/ccna/ipv6/stateless-address-autoconfiguration-slaac
deemed that the lower 64 bits is a *host* address, android phones don't do DHCPv6 only SLAAC.
I think is to ban the misers.
still too many 'guru/wizard' level stuff to figure out

i
if the miser really give you 1 out of 340,282,366,920,938,463,463,374,607,431,768,211,456 ( even toto is more generous) address, then you need to do
NAT66 whoa another 'guru/wizard' level stuff to figure out
https://docs.fortinet.com/document/...tion-guide/627219/nat66-nat46-nat64-and-dns64
in the infant days of internet there is only NAT64, i.e. bridging the new ipv6 internet to the 'old' ipv4 'galaxy' which is the whole of the internet today. with IPv6 everyone can have their own galaxy (not just a planet or solar system)